Got this request based on the PowerShell script I wrote on how to make the “enrolled by” user in Intune member of the local admin group, but instead add the user to the Remote Desktop Users group. Which is really easy to change, but to get this to work in a good way we also need to enable remote desktop access to the device, configure Windows Firewall in a correct and secure way using the domain profile (which was added to Microsoft Entra Joined devices in December 2022).
In our scenario it was developers that wanted to remote control their own computers which could make sense. One requirement is that it’s only allowed on the corporate network, which is important because the Windows Security Baseline disables merge of local/group policy Windows Firewall rules for the public profile which is important. If we would deploy a Windows Firewall policy to enable RDP on all profiles it would also open RDP in the public profile, with 4G/5G card or direct internet access that would open RDP to Internet.
The script can be downloaded from GitHub:Intune-MEM/AddToRemoteDesktopUsers.ps1 at master · Ccmexec/Intune-MEM (github.com)
What do we need to do to enable Remote Desktop Access for the user that enrolled the device in Intune then?
- Deploy the script
- Configure Window Firewall with Network List Manager and open RDP
- Enable Remote Desktop
- Configure Remote Desktop Client to use “Web account to sign in..”
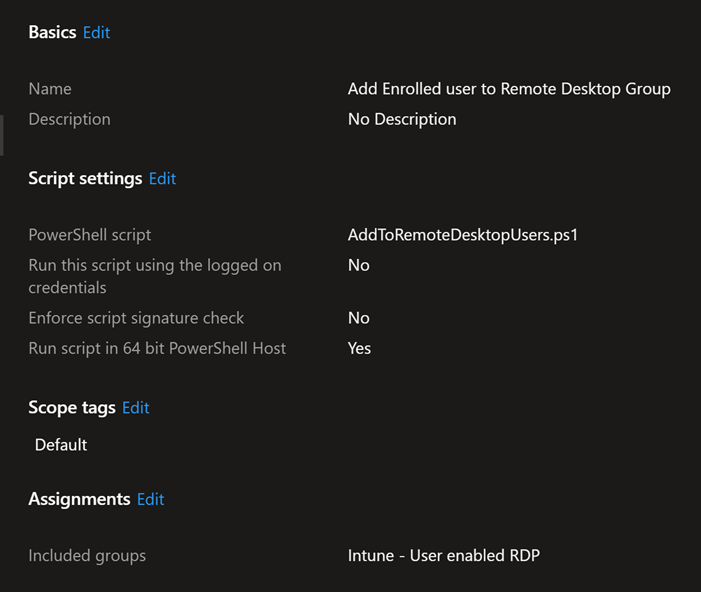
Deploy PowerShell script
I deploy it as a simple PowerShell script in Intune, it checks in the registry after the UPN of the user who enrolled the device in Intune and adds the user to the Remote Desktop Users group.
Windows Firewall
As I mentioned above it is important that we don’t enable Remote Desktop on the public Windows Firewall profile which is default for the built-in rule if that is enabled. Windows Security Baseline disables “Policy rules from Group Policy not merged” it also includes local Firewall rules.

Network List Manager can be used to enable the Domain Profile on a Microsoft Entra joined device. This is for me an important part of a Microsoft Entra Joined device design. So we actually can do some troubleshooting remotely without disturbing the end-user to troubleshoot their device.
Network List Manager is preferably configured using the Windows Firewall policy under Endpoint Security. In my case I use my Configuration Manager server as it has IIS Default website still active. The requirements for the TLS Authentication Endpoints are that it’s running HTTPS and can be validated using TLS 1.2 and does not require sign in.

We can verify this by using PowerShell:
Get-NetFirewallSetting -PolicyStore ActiveStore | Select-Object -ExpandProperty ActiveProfile

Now that we have that established, we can Enable Remote Desktop access in Windows Firewall. This is done using a simple Windows Firewall policy, were we only open it on the domain profile. I use the following settings:
Name: Enable RDP
Protocol: 6
Interface types: All
File path configured: %SystemRoot%\system32\svchost.exe
Edge traversal: Enabled
Network Types: FW_PROFILE_TYPE_DOMAIN: This value represents the profile for networks that are connected to domains.
Direction: The rule applies to inbound traffic.
Service Name: termservice
Local Port ranges: 3389
Action: Allow
Description: Remote Desktop Connection
When it is deployed to the device we can verify that the firewall is correctly configured using the Windows in Windows Defender Firewall with advanced security MMC as shown below.

Enable Remote Desktop
Settings catalog for the win! Easy to deploy the setting to enable Remote Desktop access using this setting.

Configure Remote Desktop Client to use “web account to sign in..”
This is an awesome feature which gives us the possibility to require MFA for example or whatever Conditonal Access rules we want to control access Remote Desktop. CA policies can be applied to the Microsoft Remote Desktop with ID a4a365df-50f1-4397-bc59-1a1564b8bb9c to control access to the remote PC when single sign-on is enabled.

More information can be found here: https://learn.microsoft.com/en-us/windows-server/remote/remote-desktop-services/clients/remote-desktop-connection-single-sign-on
The user will get a single-sign on experience when connecting to the remote computer if signed in with the same user. This is an awesome experience and solution.
When connecting to the device as a different user the experience is just like login in using MFA for example in any Microsoft Entra application.

2 thoughts on “Enable RDP Access Only to the Enrolled by User in Windows Using Intune”